Transaction details
Updated on 18.12.25
8 minutes to read
Copy link
Overview
When you click on any transaction row in the Transaction list, you'll see the Transaction details view for it. The Transaction details screen has five main tabs for investigating and analyzing the selected transaction - Details, Activity, Customer connections, Raw data and Analyst log.
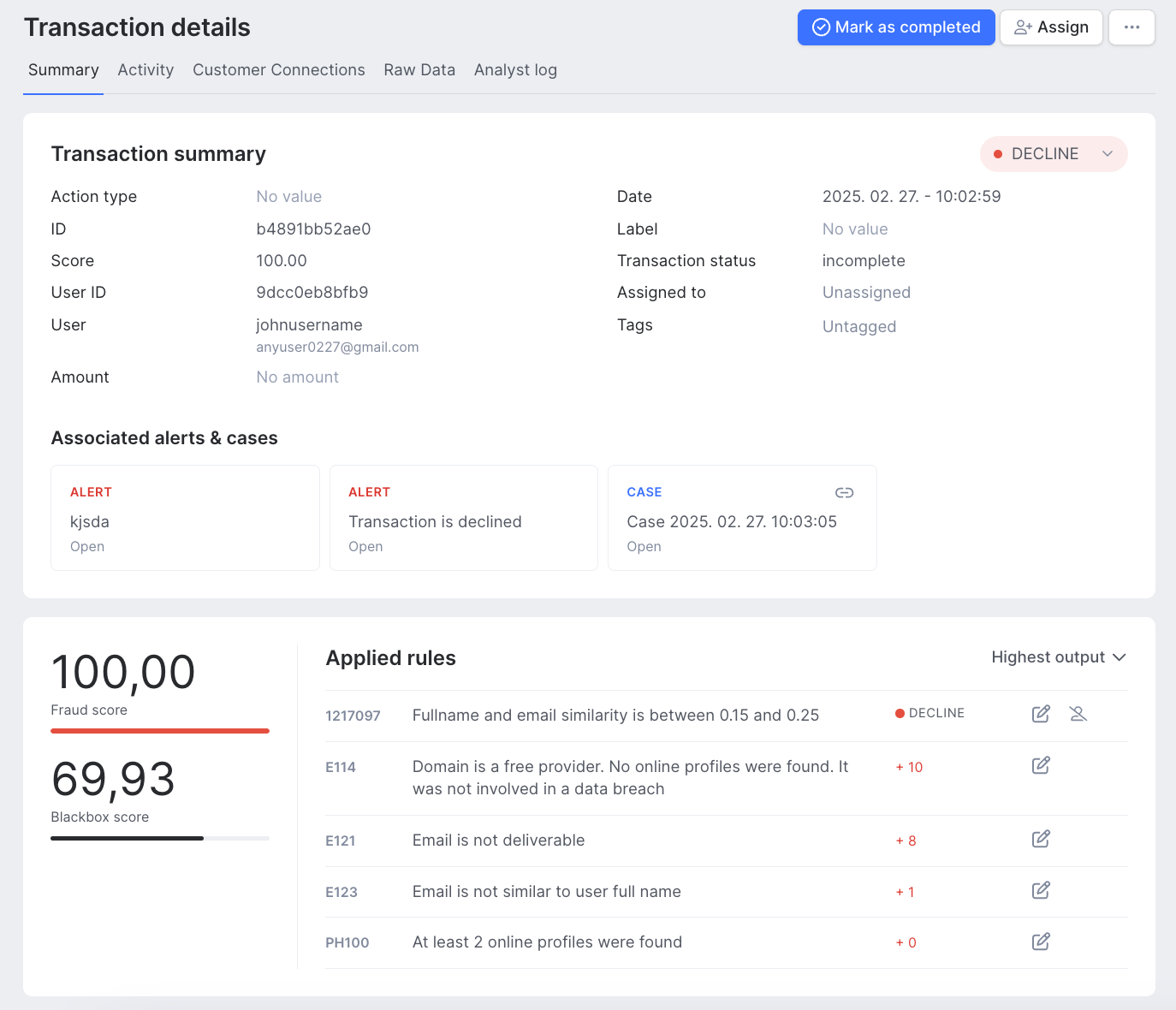
Details
All details for the selected transaction are displayed on the Transaction details screen – including raw inputs and result data from the SEON data enrichment APIs.
The top section shows key transaction information, the applied rules and the fraud score results.
You can change the state of a transaction directly from this top section, which will provide valuable feedback for our machine learning system.
The Applied rules section shows all the rules that have been triggered for a given transaction, whether they are default, custom or generated by the Machine Learning module. If a velocity rule was triggered, you will get an explanation on why this happened.
It is also possible to quickly jump to the Scoring Engine and edit an applied rule by clicking the “Edit Rule” button on the right of the relevant rule. You can also prevent a rule from being applied to the current user again with the “Exclude user from rule” feature, which will bring up a new window where you can specify the details (more on this later, in the Scoring Engine section).
Below the top section, you can find a number of sections that contain further relevant information on the selected transaction, categorized in widgets so that they are easy to review. Information is grouped into the following widgets:
Data erasure
SEON falls under the jurisdiction of the GDPR and must delete individuals' personal data on request. As a fully GDPR-compliant solution, SEON offers two methods for you to delete user data.
You can find this option at the top right corner of the page of a given transaction. Click Erase data to delete all information tied to the User ID that initiated the selected transaction.
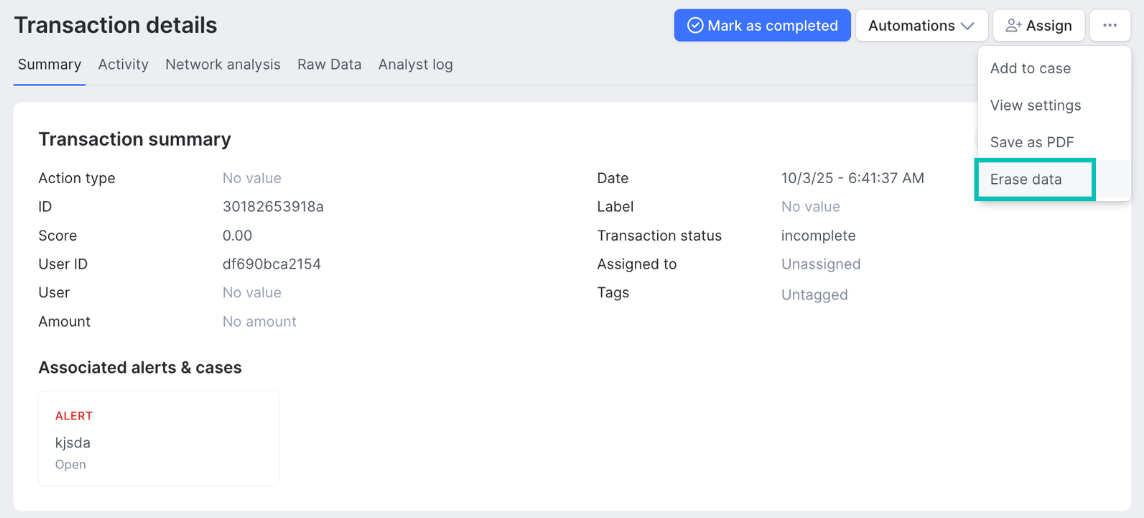
Alternatively, you can send an Erase API request to delete personal data. The API will delete everything tied to the provided user ID or email address.
Contact our Technical Services team if you need help with granular data erasure or want a clean slate for your account.
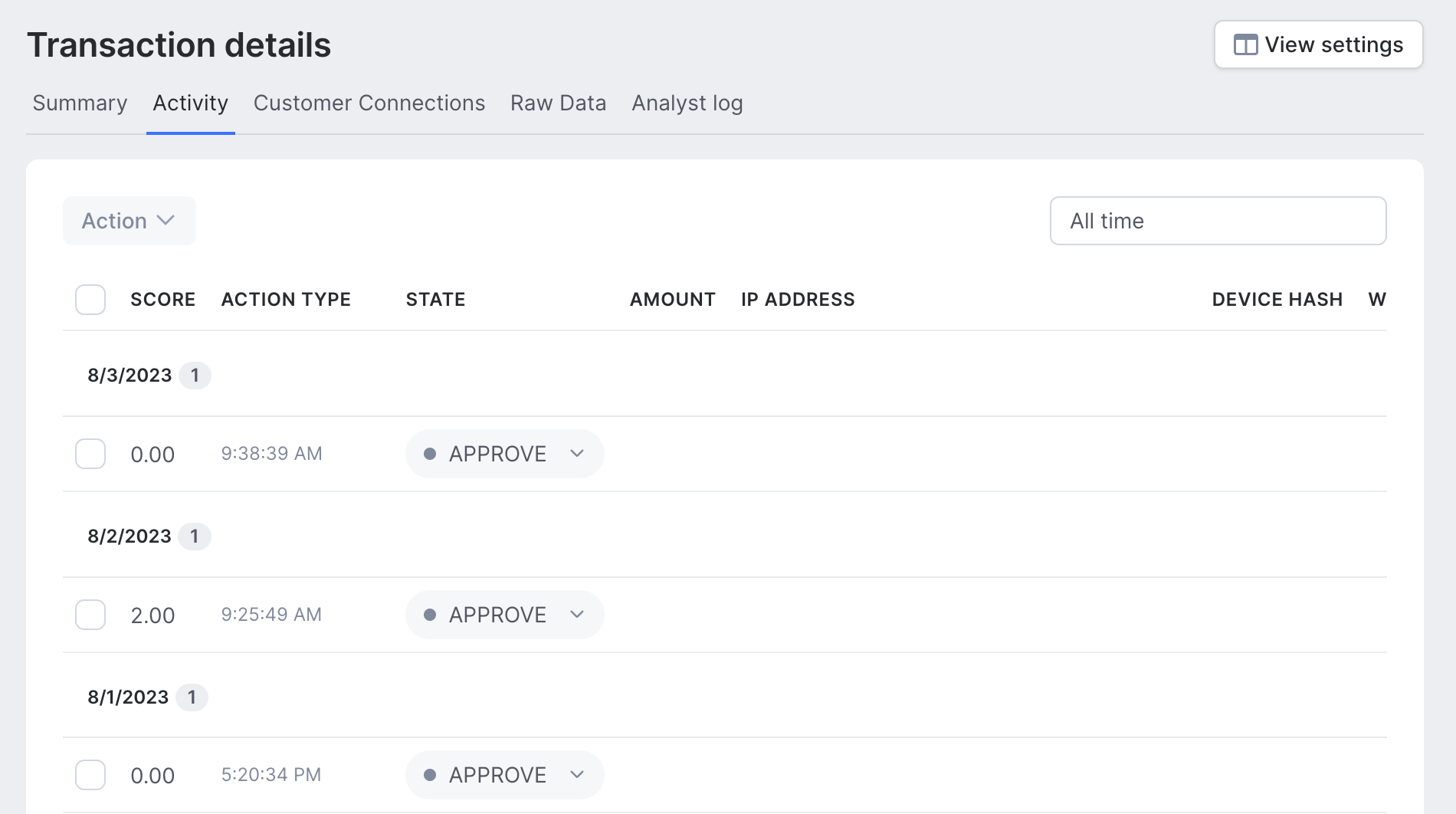
Activity
When viewing the details of a transaction, all historical transactions for the same customer can be seen on the Activity tab, which you can access at the top of the screen.
This view shows the details of each transaction. You can also update the state of each transaction directly from here.
The type of transaction can be selected from the dropdown above the column headers. Additionally, you can change the date range shown to either see all transactions or those within the last 30 or 7 days.
You can customize this screen to show specific columns of data by clicking the View settings button.
Clicking on a specific transaction will update the Transaction Details tab to show the selected transaction.
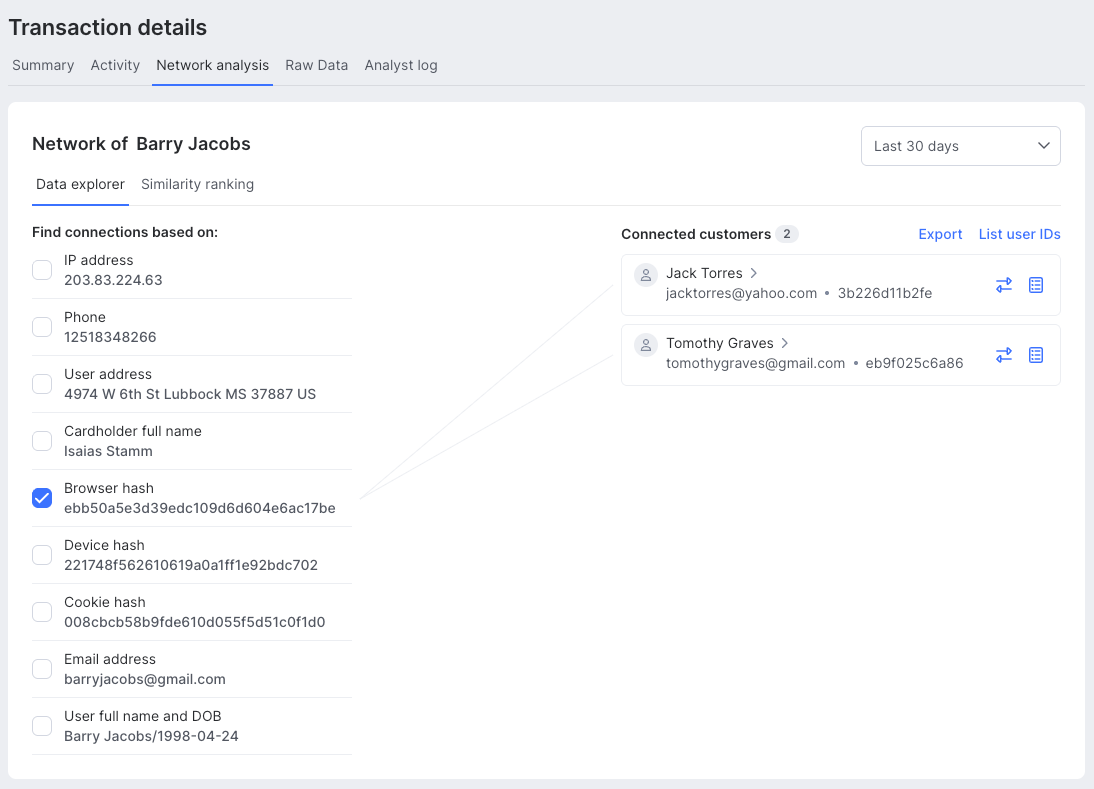
Network analysis
The Network analysis tab allows you to investigate the data relationships between the customer for the current transaction and other related customers.
You can tick the checkboxes next to the values you want to see connections for. Deep-dive into connections between the following data points:
|
|
If you select multiple data points, only those that share all selected values with the currently selected customer will be displayed.
By clicking on the Blacklist or Normal buttons next to connected customers, you can easily add them to the block list or remove them from it. If multiple, fraudulent accounts are identified, they can all be added or removed by using the Ban all or Restore all options.
The time interval for identifying matching connections can be changed by using the filter options at the top of the screen.
Raw data
The raw data tab allows you to see the actual API request and response for the selected transaction. This can be useful for data and/or integration investigation purposes.
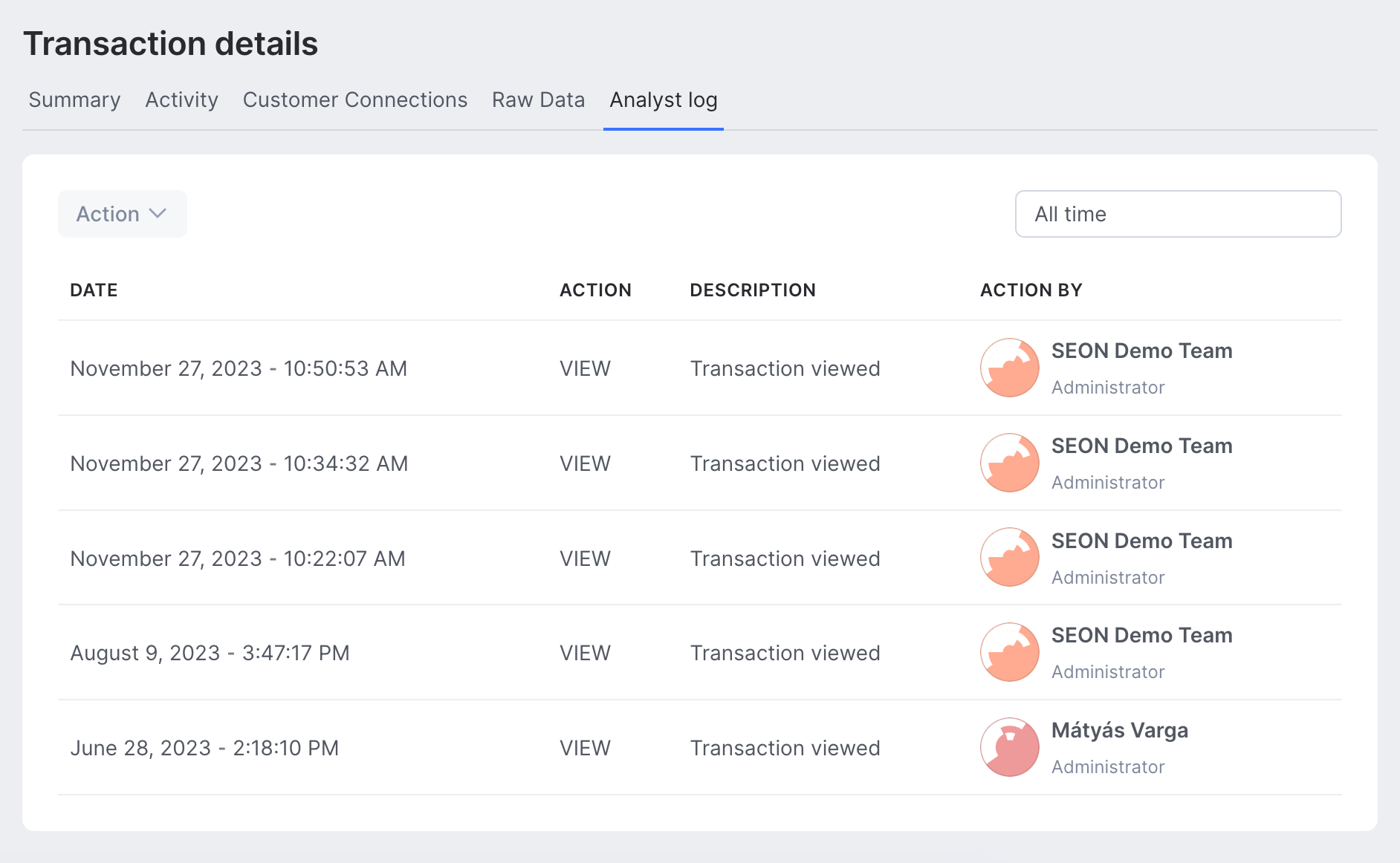
Analyst log
The Analyst Log screen shows an audit trail of all actions related to the transaction made by admin users.
All action types are shown in the listing by default, however, the list can be filtered by using the Action Type dropdown. You can also change the date range shown, using the date filter at the top right of the screen.